Critical Steps to Follow
Recycling hard drives is an important step in minimizing electronic waste and protecting the environment. Here are the steps you can follow to recycle hard drives responsibly:
-
Back Up Data
Before recycling a hard drive, it’s essential to back up any data you want to keep. You can transfer your files to an external hard drive, a cloud storage service, or another computer. Ensure that you’ve copied everything you need because once the hard drive is recycled or destroyed, data recovery becomes nearly impossible.
-
Data Erasure
Also known as data wiping or data sanitization, is the process of securely and permanently removing all data from a storage device, such as a hard drive, solid-state drive (SSD), USB flash drive, or memory card. The primary goal of data erasure is to ensure that no trace of the original data remains on the storage media, making it virtually impossible for anyone to recover sensitive or confidential information. Here are some key aspects of data erasure:
-
Methods of Data Erasure
- Overwriting: The most common method of data erasure involves overwriting the existing data on the storage device with random or predetermined patterns of 1s and 0s. Multiple passes of overwriting are often used to make data recovery more challenging.
- Cryptographic Erasure: Some methods use encryption to render data unreadable without the appropriate decryption key. When the key is deleted or inaccessible, the data becomes effectively erased.
-
Importance of Data Erasure
- Data erasure is essential for protecting sensitive information, especially when disposing of or repurposing storage devices. It helps prevent data breaches, identity theft, and unauthorized access to personal or corporate data.
- Many data protection regulations and privacy laws, such as GDPR in Europe and HIPAA in the United States, require organizations to implement secure data erasure practices to comply with data protection standards.
-
Certified Data Erasure Software
- Certified data erasure software is specifically designed to meet recognized standards for secure data erasure. These standards often include verification procedures to ensure the successful erasure of data.
- Some widely recognized certification standards include NIST 800-88, DoD 5220.22-M, and Blancco, among others. Using certified software can provide assurance that data has been properly erased.
Data Erasure in Different Scenarios
- Personal Use: Individuals often use data erasure software when they want to sell, recycle, or donate their old computers or storage devices. This ensures that personal data is not accessible to others.
- Business and Enterprise: Organizations use data erasure in various scenarios, such as retiring old equipment, transferring devices to new users, or disposing of obsolete hardware. Proper data erasure is essential for safeguarding customer and business data.
-
Data Erasure vs. Data Deletion
- Data erasure goes beyond simple data deletion or formatting, which can often be easily recovered using data recovery tools. Erasure is designed to make data recovery nearly impossible.
-
Physical Destruction vs. Data Erasure
- In some cases, especially when hardware is damaged or no longer usable, physical destruction (e.g., shredding) may be chosen over data erasure to ensure data security.
- However, data erasure is preferred when the hardware is still functional, as it allows for recycling and reuse of the equipment.
-
Data Erasure Tools
- Various data erasure tools and software solutions are available, ranging from free open-source options like DBAN to commercial software with advanced features and certifications.
- Popular commercial data erasure software includes Blancco, Secure Erase, and KillDisk, among others.
- It’s important to note that the effectiveness of data erasure depends on the method used and the quality of the software or tools employed. For organizations and individuals handling sensitive information, using certified data erasure methods and software is highly recommended to ensure compliance with data protection laws and to protect data privacy.
-
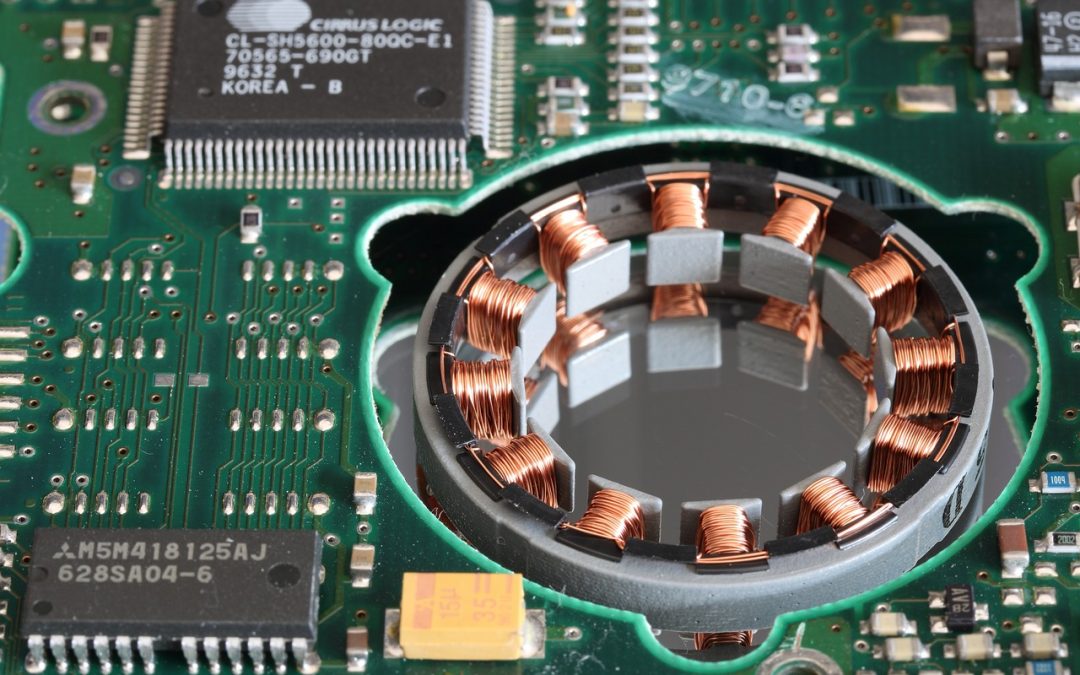
Physical Destruction
Physical destruction is a method of rendering storage devices, such as hard drives and solid-state drives (SSDs), completely and irreparably nonfunctional to prevent any access to the data they contain. This approach is typically employed when data security is of utmost importance, and there is a need to ensure that the data cannot be recovered under any circumstances. Here are key aspects of physical destruction:
-
Methods of Physical Destruction
-
Hard Drive Shredding
This is one of the most common methods for physically destroying hard drives. Specialized shredding machines are used to shred the hard drive into small pieces, rendering it unusable. The resulting fragments are often sent for recycling.
-
Drilling
Drilling holes through the hard drive’s platters is another method. This process creates physical damage to the storage medium, making data recovery virtually impossible.
Crushing
Some facilities use hydraulic presses or crushers to physically deform and crush hard drives, ensuring they are beyond repair.
-
Incineration
In certain cases, hard drives are incinerated at high temperatures to melt and destroy all components, including the platters and circuitry.
-
-
When to Choose Physical Destruction
-
Physical destruction is chosen when data security is the top priority, and there can be no risk of data recovery. It’s often used in situations where data breaches could have severe consequences, such as in the healthcare, financial, or military sectors.
-
It’s also a suitable option when hard drives are no longer usable due to damage or end-of-life and cannot be effectively wiped or sanitized.
-
-
Data Recovery Prevention
- Physical destruction ensures that the storage medium is irreparably damaged, making it impossible for any data recovery methods, including forensic techniques, to retrieve information from the device.
-
Environmental Considerations
- After physical destruction, the remnants of the storage devices are often sent for recycling. This process recovers valuable materials like metals, plastics, and glass, minimizing the environmental impact of electronic waste.
-
Certification and Documentation
- In some cases, organizations may require certificates of destruction as proof that the physical destruction process was carried out in compliance with data security regulations and standards.
-
Secure Handling and Disposal
- It’s crucial to ensure that the physical destruction process is carried out securely and that all remnants of the destroyed hardware are handled and disposed of responsibly, especially if there are hazardous materials involved.
-
Cost Considerations
- Physical destruction methods may involve additional costs, such as the use of specialized equipment or third-party services, compared to data erasure. However, for organizations with stringent data security requirements, these costs are often considered necessary.
-
Hard Drive Enclosures and Components
- When destroying hard drives, organizations should also consider what to do with any associated enclosures, cables, and connectors. These components can contain sensitive information and should be securely disposed of or recycled as well.
-
Find a Recycling Center
- Look for a reputable e-waste recycling center in your area. Check their website or contact them directly to confirm that they accept hard drives. Ensure they have the necessary certifications for responsible e-waste handling.
-
Check for Pickup Services
- Some e-waste recycling centers offer pickup services for larger quantities of electronics or for those who can’t transport the equipment themselves. Inquire about this option if it’s more convenient for you.
-
Prepare the Hard Drive
- Before dropping off the hard drive, it’s a good practice to label it as “recycled” or “destroyed” to prevent it from being mistakenly reused or resold.
- You can remove screws, enclosures, or connectors if you plan to reuse them or recycle them separately.
-
Drop Off or Arrange Pickup
- Follow the instructions provided by the recycling center for dropping off your hard drive. If they offer a pickup service, schedule a convenient time for them to collect it.
-
Obtain a Certificate of Destruction
A certificate of destruction is a formal document that provides evidence that specific items, often sensitive or confidential in nature, have been properly destroyed or disposed of in accordance with established guidelines or regulations. These certificates serve as a record and proof that the destruction process was conducted securely and in compliance with legal and ethical standards. Here’s more information about certificates of destruction:
Purpose of a certificate of destruction
-
Data Security
Certificates of destruction are commonly associated with the secure disposal of sensitive data, such as personal information, financial records, medical records, or classified documents. They offer assurance that the data is no longer accessible or recoverable.
-
Compliance
In many industries and for certain types of data, there are legal and regulatory requirements governing how data must be disposed of. A certificate of destruction helps organizations demonstrate compliance with these requirements.
-
1. Protection against Liability
Having a certificate of destruction can protect organizations from liability in case of data breaches or unauthorized access to sensitive information.
2. Contents of a Certificate of Destruction:
The exact contents of a certificate of destruction can vary depending on the specific circumstances and the organization issuing it. However, typical elements include:
Date of Destruction
: The date when the destruction process occurred.
-
Description of Items Destroyed
: A detailed list of the items or materials that were destroyed, including serial numbers or unique identifiers where applicable.
-
Method of Destruction
Information about how the items were destroyed, whether it was through shredding, incineration, crushing, data wiping, or another method.
-
Location of Destruction
The physical location where the destruction took place, often specifying the facility or service provider responsible for the process.
-
Witnesses
: Some certificates include the names and signatures of witnesses or individuals responsible for overseeing the destruction.
-
Certification Statement
: A statement certifying that the destruction was carried out in accordance with applicable laws, regulations, and industry standards.
-
Identification
The certificate may include identification information about the organization responsible for the destruction, such as its name, contact information, and any relevant certifications or licenses.
3. Use Cases for Certificates of Destruction:
-
Data Destruction
Certificates of destruction are frequently issued for the secure disposal of electronic media, including hard drives, SSDs, and other storage devices.
-
Paper Documents
In the case of paper documents, especially those containing sensitive information, certificates of destruction are used to verify that the documents have been securely shredded or incinerated.
-
Confidential Materials
Organizations dealing with confidential materials, such as law firms, medical facilities, and financial institutions, often require certificates of destruction for compliance and accountability.
-
Obsolete Equipment
Certificates may also be used when disposing of obsolete or end-of-life equipment to ensure that no data or proprietary information remains on the devices.
4. Legal and Compliance Considerations
It’s important for organizations to be aware of and adhere to relevant laws and regulations regarding the disposal of sensitive data. The issuance of a certificate of destruction can demonstrate a commitment to legal compliance and data security.
In summary, a certificate of destruction is a formal document that provides evidence that sensitive items, including data or physical materials, have been securely and properly destroyed. It plays a crucial role in data security, compliance, and liability protection for organizations that handle sensitive information.
-
-
Environmental Responsibility
- Reputable e-waste recycling centers ensure that electronic waste is disposed of responsibly. This includes safely managing hazardous materials and recovering valuable materials like metals, plastics, and glass for recycling.
-
Consider Donation
- If your hard drive is still in working condition and relatively new, consider donating it to a nonprofit organization, school, or community group. They may be able to use it for their computer needs, which can extend the lifespan of the equipment.
- By following these expanded guidelines, you can contribute to both data security and environmental sustainability when recycling hard drives. Responsible recycling of electronic waste is crucial to protect personal information and reduce the environmental impact of electronic devices, it also prevents private data getting into the wrong hands and gives you peace of mind.

Recent Comments